Two-Factor Authentication is the Future
By Sean Marshall
November 2, 2019, 2:00pm
In today’s digital climate, online security is of upmost importance and therefore two-factor authentication (2FA) has become increasingly prevalent. In the past, this issue of security had primarily been managed with the use of passwords – allowing to users to access a variety of personal accounts online. However, this single layer of defence has proven to be ineffective in preventing account takeover. 2FA on the other hand, provides an added layer of protection, involving a more robust two-step verification process (Kemshall 2011). 2FA methods require users to not only enter their password, but a second factor also. This second factor can be something unique to them, such as a fingerprint or a face-scan. Combining these two layers of security greatly increases user protection and decreases the likelihood account takeover. For this very reason, 2FA is very important.
Are Passwords ‘enough’ Anymore?
With hackers and data breaches constantly making headlines, it is integral that internet users protect themselves adequately (O’Neill 2019). 2FA certainly has its pitfalls, however, it certainly trumps the standard use of passwords alone. Although 2FA is hardly a new concept, numerous organisations are beginning to incorporate it as an additional security layer for users. These organisations include social media giants such as Instagram, Facebook and Twitter, as well as several online banks (Barrett 2018). Despite this step in the right direction, there is a far more prominent verification method used online (Kemshall 2011). This is the old fashioned username and password combination which is commonly applied as the only form of verification. This familiar process is referred to as single factor authentication (SFA). This archaic method has substantial drawbacks, especially when considering cybercriminals ever-improving hacking techniques (Kemshall 2011).
With the rise of smartphones, everything online is significantly more accessible. Online users have easy and convenient access to online shopping, video streaming services, social media platforms and even sites/applications associated with work and school. Resultantly, the average online consumer has numerous accounts - all of which requiring login details. However, to simplify things, plenty of online users (more than 80% of people between 18-30) are guilty of using the same password across a vast array of sources (Zoir 2018). This common and flawed practice makes things substantially easier for hackers. This is because they can now gain access to all of a user’s accounts upon figuring out their password. Another mistake made by users, is the use of weak passwords which can easily be guessed or cracked (Gunson et al. 2011).
As a result, SFA has resulted in a devastating amount of breaches. Amongst these are the infamous Target and Neiman Marcus data breaches which occurred in holiday season 2014. These massive security breaches impacted upwards of 70 million customers (Hollister 2014). This alarming event left critical information such as customer credit and debit cards exposed to potential misuse and theft. The flaws of single-factor authentication do not end there, however. Due to SFA ‘the number of hacks in 2017 increased by an average of 27 percent when compared to the previous year’ (Brown 2018). Also, it was found that 81 percent of network breaches were assisted by user’s poor credentials. Clearly, this information highlights that it is becoming unwise to rely on traditional passwords alone. They simply do not provide a sufficient level of security. Two-factor authentication on the other hand is a more reliable alternative, increasing security for online users and large corporations alike.
The Future: Two-Factor Authentication
Although far from perfect, two-factor authentication is far more secure when compared to single-factor authentication (O’Neil 2019).This is because 2FA creates another obstacle for hackers, thereby increasing user security. When verifying a user’s identity 2FA typically involves three distinct methods – knowledge, possession and inheritance (Zoir 2018). ‘Knowledge’ refers to something that only the user knows, such as a password or security pin (Gunson et al. 2011). This is essentially the entirety of the single-factor authentication method. Alternatively, the ‘possession’ method refers to something only the user possesses (Gunson et al. 2011). This includes physical items such as smartphones, SIM cards and USB security keys. Finally, the ‘inheritance’ method involves something unique to the user, such as a fingerprint or iris scan (Gunson et al. 2011).
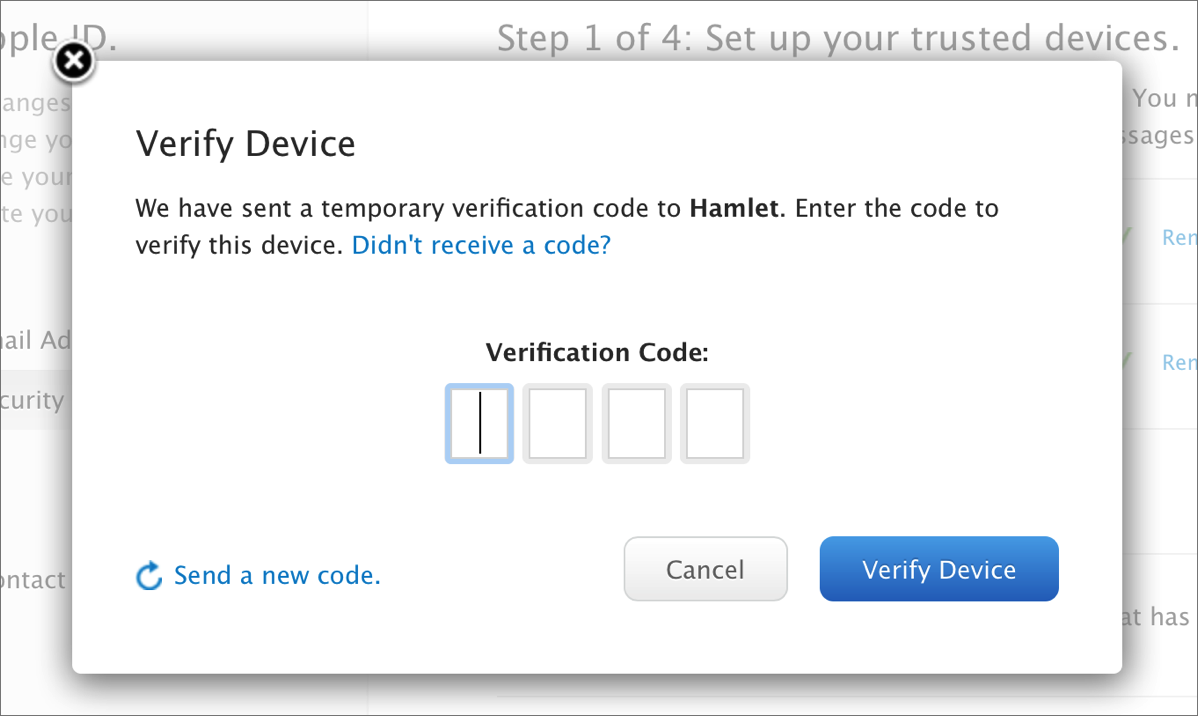
One of the most common forms of two-factor authentication combines aspects of ‘knowledge’ and ‘possession’. This is achieved through the use of SMS codes. In this method, a user will enter their password and promptly receive an SMS code from the relevant service (Barrett 2018). This is a one-time code which is sent to a user’s phone number whenever they log in from a new device. This makes it far more difficult for hackers to gain access to accounts. Even if they were to acquire a user’s password, they would still require access to text messages in order to takeover an account. According to studies, SMS codes have enabled 100 percent of automated account takeover attempts to be prevented (O’Neill 2019). Additionally, they have prevented 96 percent of bulk phishing attacks (fraudulent practice where users are conned into giving away personal information) and 76 percent of targeted attacks (O’Neill 2019). Another positive about SMS codes is that they are inexpensive, easy to use and convenient in modern times where people always have their smartphone nearby (Kemshall 2011).
Nevertheless, there are far more secure methods of two-factor authentication which exist. Arguably the most effective 2FA method involves the use of a security key – once again combining aspects of ‘knowledge’ (passcode/password) and ‘possession’ (physical security key). A security key is a small and affordable device which can be connected to systems via USB-A, USB-C and Bluetooth (Colt 2018). These keys are manufactured by the likes of Google, Yubico, Feitian and more (O’Neill 2019). Security keys are far more effective than SMS codes as they provide an additional layer of hardware protection which is almost impenetrable (Barrett 2018). According to Google, since they began using security keys not a single Google employee has experienced an account takeover (O’Neill 2019). Additionally, a year-long study showed that security keys helped prevent a 100 percent of account takeover attempts (all types) (O’Neill 2019). With these factors considered, it is clear why journalists, politicians and human rights defenders choose to use security keys. For these people, ‘cybersecurity can be a matter of life and death’ and security keys are simply the most robust form of protection available (O’Neill 2019).
In summation, it is evident that not all 2FA offers equal levels of protection. However, it is extremely apparent that all forms of 2FA easily trump SFA.
The Problem With 2FA
Despite the fact that 2FA is extremely helpful it also has its fair share of downsides. One minor drawback is that it can complicate and lengthen the traditional process of logging into an account (SFA) (Kemshall 2011). This means it can occasionally be inconvenient for users. However, this issue can certainly be overlooked. This is because two-factor authentication is a significantly more secure method of verification when compared to traditional SFA.
Another issue with 2FA is the numerous downsides that come with the use of SMS codes. In fact, SMS codes are commonly regarded as the weakest form of two-factor authentication. This is because the verification codes are sent across a network, giving hackers the ability to intercept them and thereby takeover an account (Brown 2018). Hackers also have the ability to hijack smartphone SIMs. This gives them access to user phone numbers and allows them to redirect any two-factor notifications to their own device, thereby simplifying account takeover (Barrett 2018). Taking advantage of SMS code 2FA vulnerabilities, a hacking ring was able to steal upwards of $2.4 million in cryptocurrency (Lecher 2019). Besides these huge problems there are also minor downsides regarding SMS 2FA. Firstly, companies issuing these codes must pay SMS sending fees, therefore it is not very cost-effective for them. Another issue is that it cannot be used without cellular coverage, making it undesirable for use in remote or rural areas. Finally, SMS code 2FA requires a user to have their phone on them. This means it is impossible to use if their phone is dead, stolen or lost. When considering these factors, it is understandable why this form of two-factor authentication is often advised against.

Moreover, there are several downsides to security keys as well. Unlike, SMS code 2FA which is essentially free, security keys can be rather costly. This is quite unideal as users must invest between $20 and $60 to ensure they are protected (Colt 2018). Another issue with security keys is that they can easily be misplaced, opening up opportunities for theft.
Furthermore, one of the greatest pitfalls regarding 2FA is that is not a 100 percent full proof. As technology rapidly improves, cybercriminals will continue to find kinks and vulnerabilities which allow them to bypass security. Even now, hackers are able to penetrate security using malware, phishing, SIM hijacking, interception and plenty other methods. Regardless, 2FA has definitely proven itself to be a better alternative to SFA.
The Final Verdict
In today’s technological climate it is becoming abundantly clear that passwords no longer offer enough protection. Failure to consider this has resulted in widescale data breaches which have affected millions of people. In order for online users to protect themselves it is essential they utilise two-factor authentication. Compared to standard SFA it offers far more protection. Additionally, it is supported by the likes of Facebook, Instagram and Twitter along with most large enterprises. However, it is important to note that two-factor authentication comes with its own flaws. Despite this, it is still a great alternative to SFA.